Security Concerns Surrounding the Apple Podcasts App
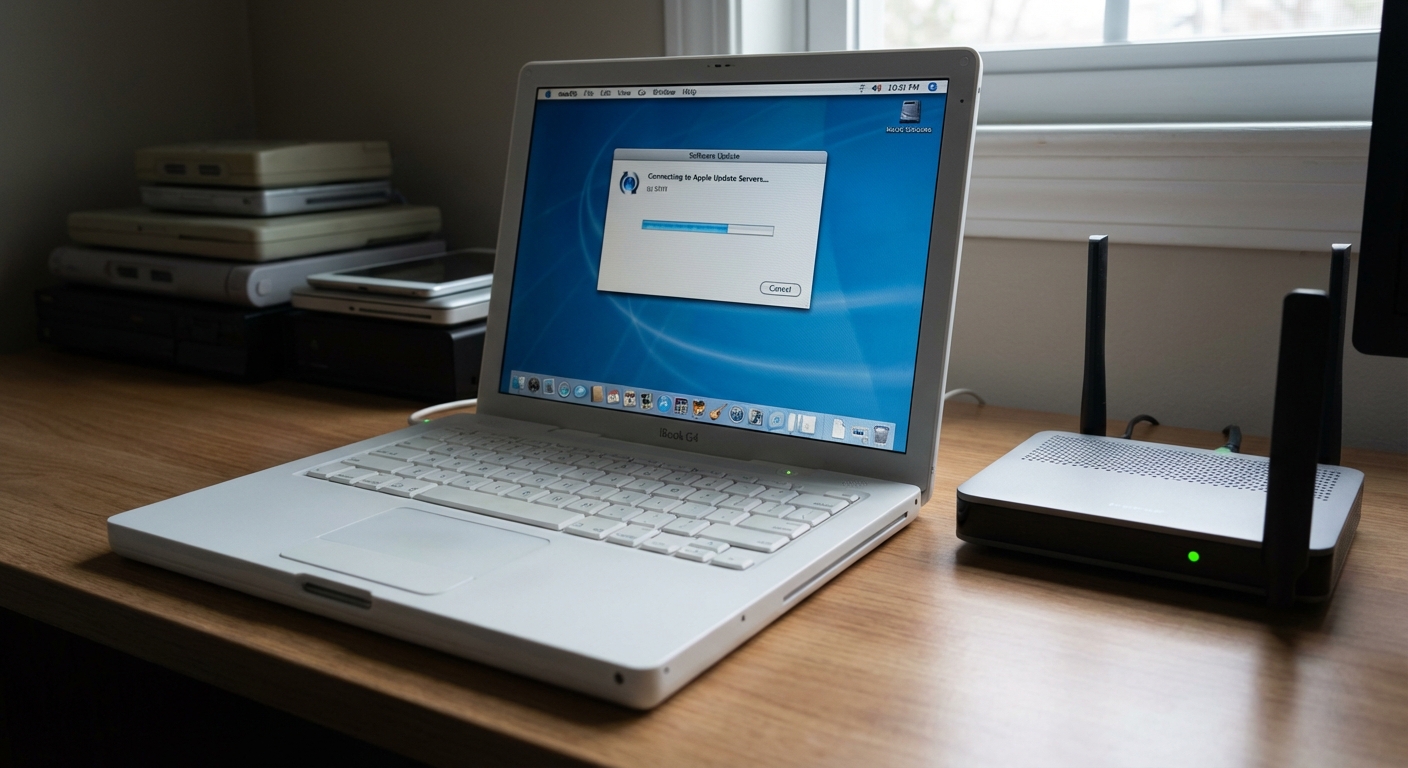
Security researchers have detected suspicious activity in the Apple Podcasts app, which might be used to deliver malicious content to users.  Created by Gemini, Joseph Cox from 404Media shared how he noticed something strange happening with this app. In recent months, he found that both the iOS and Mac versions of the Podcasts app were mysteriously opening podcasts related to religious, spiritual, and educational themes without any apparent reason.
Created by Gemini, Joseph Cox from 404Media shared how he noticed something strange happening with this app. In recent months, he found that both the iOS and Mac versions of the Podcasts app were mysteriously opening podcasts related to religious, spiritual, and educational themes without any apparent reason.
Sometimes, when I unlock my computer, the app starts up and displays one of these peculiar podcasts. Additionally, at least one podcast page in the app contains a link to a potentially malicious site. Another podcast, named in Arabic roughly translating to ‘Words of Life’, featured someone’s Gmail address. Sometimes the podcasts have actual sound, such as a religious sermon, while other times they are completely silent. Although the podcasts are often several years old, they are only just now being shown to me.
The author tested one of the podcasts and discovered a link in the description. This link attempts to direct listeners to a website that tries to execute a cross-site scripting (XSS) attack. This attack involves a hacker embedding their malicious code onto a seemingly normal website. The link is located in the ‘Show Website’ section of the podcast page. Clicking on it redirects to another site, followed by a pop-up with the message ‘XSS. Domain: domain name’.
Expert Opinions and Ongoing Concerns
Interestingly, a review of the Podcasts app exposed another person encountering the same issue, questioning how Apple permits XSS attacks.
The author consulted macOS security expert Patrick Wardle, who noted that the main issue with podcasts is that they can be launched directly via a link from any other site, whereas third-party apps would need confirmation to run.
I replicated similar behavior, though through a website: simply visiting a website can launch podcasts (and download a podcast selected by an attacker), requiring no user prompts or approvals, unlike other external applications on macOS (e.g., Zoom).
Of course, it’s essential to highlight that this is not an attack by itself. However, it creates a very efficient delivery mechanism if there is indeed a vulnerability within the Podcasts app. It remains unclear if these attempts have been successful, but the level of scrutiny indicates that attackers actively assess the Podcasts app as a potential target.
Efforts for Response and Future Prevention
Wardle mentioned he has been trying to contact Apple for several months about this issue, but the company remains unresponsive. Perhaps they will react now that the information has reached the media.